最近这几天,的确是没什么时间来写点东西,每天都在与代码拼命抗争。另外就是之前处理的服务器被入侵貌似远没结束,还有一些乱七八糟的东西需要处理。
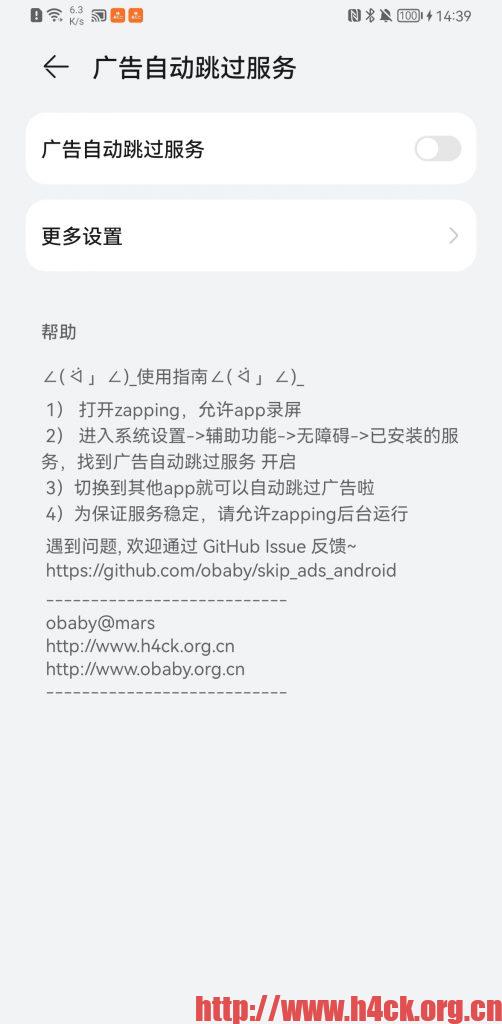
Android Skip Ads Android Project【截屏部分】
作为安卓自动跳过广告三部曲的第二部分,主要是实现系统截屏功能。继《Android Skip Ads Yolov5 Project》之后,下一步就是获取当前屏幕的截图,把截图传入分析引擎实现广告跳过按钮的识别,最后一步是按钮点击。
要在安卓系统上实现截图(截取整个屏幕,并且需要截取其他app的界面),通常有下面三个方法:
1.直接调用系统的截屏工具,需要root权限
adb shell screencap -p /sdcard/sreenshot1.png
从com.alibaba.wxlib.exception.WXRuntimeException: should call prepareTargetKey first 说起
对于安卓的开发,我并没有太多的经验,并且很多的东西目前也没有深入的研究。最近在更新Findu的安卓版本的时候,出现了一个意外的错误。错误代码如下:
03-07 15:03:30.046 12215-12290/today.findu.findu.alibaba.openIMUI:watchdog E/AndroidRuntime: FATAL EXCEPTION: initFeedbackThread Process: today.findu.findu.alibaba.openIMUI:watchdog, PID: 12215 com.alibaba.wxlib.exception.WXRuntimeException: should call prepareTargetKey first at com.alibaba.mobileim.utility.AccountInfoTools.initTargetAppKeys(AccountInfoTools.java:190) at com.alibaba.mobileim.FeedbackAPI.initFeedbackImpl(FeedbackAPI.java:108) at com.alibaba.mobileim.FeedbackAPI.access$000(FeedbackAPI.java:38) at com.alibaba.mobileim.FeedbackAPI$1.run(FeedbackAPI.java:97) at java.lang.Thread.run(Thread.java:761)
并且同时还有大量的其他的错误信息:
03-07 15:03:34.274 12215-12215/today.findu.findu.alibaba.openIMUI:watchdog E/security: [2014@taobao_h5_3.0.0][WLqJSW6PXu8DAOb+xk4MZjLO][] : *********************************************************** 错误编码 = 10010 错误消息 = 发生错误,消息为 null sec code 162, 请使用 LogCat 查看更多细节 解决建议 = 请使用默认的 androiddebugkey 对当前开发应用签名或在应用初始化之前调用 AlibabaSDK.turnOnDebug(), 运行程序查看 logcat 输出以获取更多错误细节,并采取对应操作 错误堆栈 = ErrorCode = 162 com.alibaba.wireless.security.open.SecException at com.alibaba.wireless.security.open.initialize.c.a(Unknown Source) at com.alibaba.wireless.security.open.initialize.a.a(Unknown Source) at com.alibaba.wireless.security.open.initialize.b.b(Unknown Source) at com.alibaba.wireless.security.open.initialize.b.loadLibrarySync(Unknown Source) at com.alibaba.wireless.security.open.initialize.b.initialize(Unknown Source) at com.alibaba.sdk.android.security.impl.h.a(SourceFile:23) at com.alibaba.sdk.android.security.impl.SecurityGuardWrapper.init(SourceFile:61) at java.lang.reflect.Method.invoke(Native Method) at com.alibaba.sdk.android.a.a.a.a(SourceFile:91) at com.alibaba.sdk.android.task.a.c(SourceFile:186) at com.alibaba.sdk.android.task.a.a(SourceFile:144) at com.alibaba.sdk.android.AlibabaSDK.a(SourceFile:135) at com.alibaba.sdk.android.AlibabaSDK.asyncInit(SourceFile:98) at cn.org.findu.finduUI.demo.DemoApplication.onCreate(DemoApplication.java:61) at android.app.Instrumentation.callApplicationOnCreate(Instrumentation.java:1024) at android.app.ActivityThread.handleBindApplication(ActivityThread.java:5403) at android.app.ActivityThread.-wrap2(ActivityThread.java) at android.app.ActivityThread$H.handleMessage(ActivityThread.java:1545) at android.os.Handler.dispatchMessage(Handler.java:102) at android.os.Looper.loop(Looper.java:154) at android.app.ActivityThread.main(ActivityThread.java:6119) at java.lang.reflect.Method.invoke(Native Method) at com.android.internal.os.ZygoteInit$MethodAndArgsCaller.run(ZygoteInit.java:886) at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:776)